While studying for the CCNP Route exam, I noticed that GRE Tunneling and IPSec were mentioned as topics, however configuration of the two was never really covered in the certification guide. In addition, I did not see any labs involving this type of scenario, so I decided to create my own. Hopefully this provides some insight to others about how to configure GRE Tunnels over IPsec. Don’t feel bad if this takes you a while, setting up this scenario and writing this up took a whole Saturday afternoon. The configuration files are at the bottom of the post.
IPSec can secure data in transit and provides authentication that it came from a trusted source.
To route from the branch office to the enterprise core, you can use either static routes or a routing protocol. To secure traffic over the internet, IPSec can be used. To utilize a routing protocol to connect securely to the core with IPsec, it must be combined with a GRE tunnel which supports the broadcasts/multicasts necessary for proper IGP operation.
GRE Tunnels
* Act link a point-to-point link from a Layer 3 perspective.
* Supports many passenger protocols, including IPv4.
* Encapsulates/forwards broadcasts and multicasts, therefore supporting IPv4 IGP's.
* GRE tunnels can run through IPsec tunnels.
Implementing Branch Office GRE over IPSec VPN
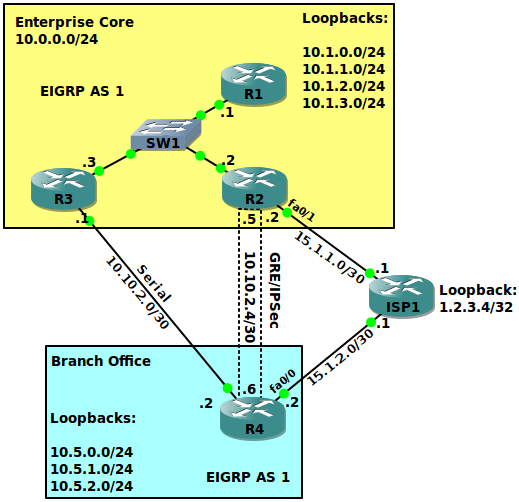
Branch Office GRE/IPSec VPN (R2-R4) & Private Serial (R3-R4)
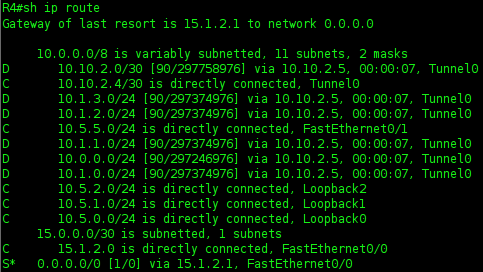
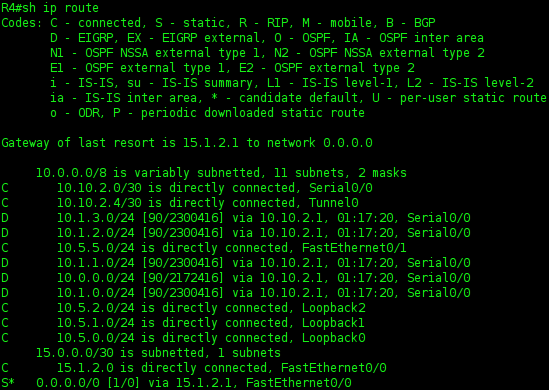
Here, we will utilize split-tunnel at the Branch Office to ensure that only traffic destined for the Core will be encrypted over the GRE IPSec tunnel. A default route is configured on R2 and R4 to ISP1. Additionally, ISP1 has been configured with a loopback to test split-tunnel functionality.
All routers (except ISP1 obviously) will participate in EIGRP AS 1. Each participating router shall be configured with the network 10.0.0.0 and **no auto-summary **commands.
Configure the GRE Tunnels on R2 and R4
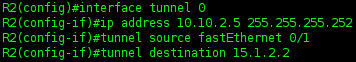
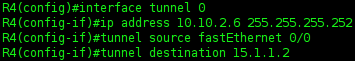
The tunnel source is the internet-facing interface, in this case fa0/0 with the IP of 15.1.1.2 on R2 and fa0/1 with the IP of 15.1.2.2 on R4. When associating a tunnel source with an interface, if the associated interface goes down, so does the tunnel. If you have redundant connections, use a loopback as a source instead.
R2 - R4 GRE Tunnel Configuration
First, configure the GRE tunnel. After doing this, you should see your EIGRP neighbors go up.
In a real world situation, you’d probably also want to configure the tunnel with Path MTU Detection. This will mitigate fragmentation issues that could cause your routers to drop CEF and use process switching. Enable PMTUD at each tunnel endpoint with tunnel path-mtu-discovery.
R2
R4
R2 GRE Route-Map
Here, we will configure a route-map to prevent a default route from ever being advertised over the GRE tunnel. The only way for R4 to ever learn R2’s default route should be via the serial connection to R3, and it should only be utilized if R4’s fa0/0 interface goes down. We could also utilize this to block other networks from being advertised over the GRE tunnel by modifying the ACL.
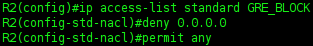
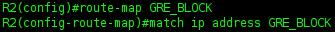
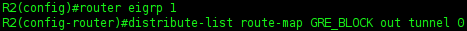
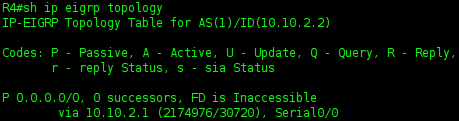
Now, you can see that R4 only learns a backup Default-Route through R3. Previously, it learned it through the tunnel as well, which would be silly to utilize and might break split-tunnel if the static default-route was lost for some reason.
Encrypt GRE Tunnel traffic using IPSec
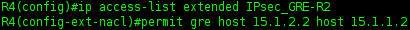
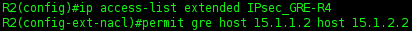
We will now encrypt traffic traversing the GRE tunnel using IPsec. We must first define an ACL to catch the traffic we wish to encrypt, which will be GRE traffic from our GRE source-interface destined for the GRE tunnel destination.
R2 IPsec Policy Creation
ACL (Catch GRE to R4)
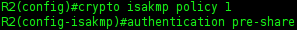
ISAKMP Policy
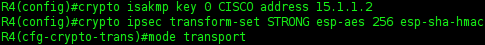
ISAKMP Key & IPSec Transform Set (Transport Mode)
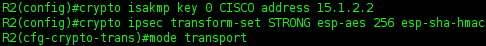
_Keep in mind that transport mode is used only because we are not traversing NAT, we are going from R2 to R4’s public IP for both IPSec and GRE Tunnels. _Tunnel mode is required if the GRE destination is different from the IPSec destination. If the endpoints were each behind a NAT router, the situation requires a combination of NAT-T and Tunnel Mode. Tunnel mode adds an extra 20 bytes to the overall packet size. NAT-T also adds an extra 20 bytes per packet and encapsulates the IPSec traffic into UDP packets over port 4500.
Crypto Map Configuration
Here, we configure the Crypto Map to R4. We will use the previously created GRE catching ACL.
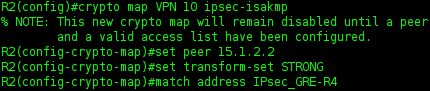
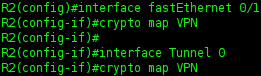
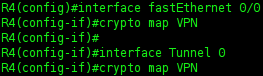
Apply Crypto Map to GRE Tunnel
The Crypto Map should be applied to the physical exit interface. Cisco recommends applying it to the logical tunnel interface as well.
R4 IPsec Policy Creation
We will follow the same procedure utilized on R2 and reverse the IP addresses.
ACL (Catch GRE to R2)
ISAKMP Policy
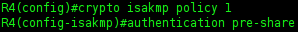
ISAKMP Key & IPSec Transform Set (Transport Mode)
Crypto Map Configuration
Here, we configure the Crypto Map to R4. We will use the previously created GRE catching ACL.
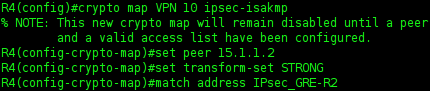
Apply Crypto Map to GRE Tunnel
Verify IPsec and Split-Tunnel Functionality
You can utilize Wireshark to verify only ESP traffic traverses between the GRE endpoints. I found that the Crypto Map did not need to be applied to the logical Tunnel 0 interface to function, but only the physical exit interface. I am not sure why Cisco recommends applying it to both.
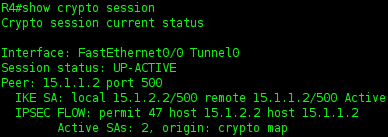
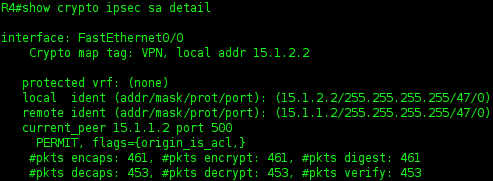
You can see that the Crypto traffic for Tunnel 0 and FastEthernet 0/0 is identical. I am not sure if running the crypto map VPN on both the Tunnel 0 and FastEthernet 0/0 is causing excess encryption overhead, or if it only encrypts the traffic once.
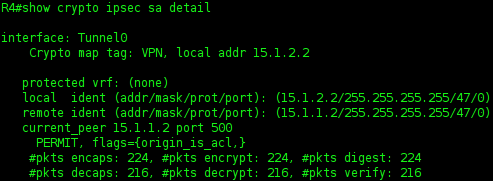
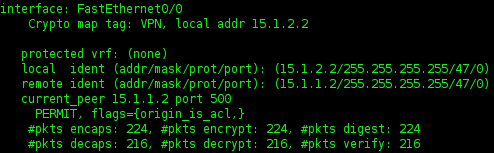
After disabling Crypto Map VPN on the Tunnel 0 interface, I confirmed via Wireshark that the GRE traffic continued to be encrypted. A show crypto ipsec sa detail shows that the traffic continues to be encrypted as well.
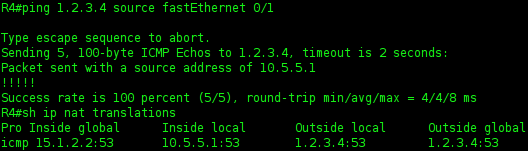
Verify Split-Tunnel
To test this, I will simply ping a simulated public internet address of 1.2.3.4 from the inside interface of R4.
Conclusion
We have implemented remote branch office with redundant connectivity to the core; a leased line and a secured backup utilizing GRE over IPsec via the public Internet. Our branch office is now able to participate in the EIGRP routing process over either link. If you wanted to use the IPsec VPN as your primary connection to HQ, modify the bandwidth value of the Tunnel 0 interfaces to make the EIGRP metric more preferable than the serial route. By default, tunnel interfaces seem to be given a bandwidth value of only 9kbps. The default delay value of tunnel interfaces is high as well. Tweak the bandwidth and delay values to achieve desired results.
Normal Conditions
Downed Serial Link to HQ